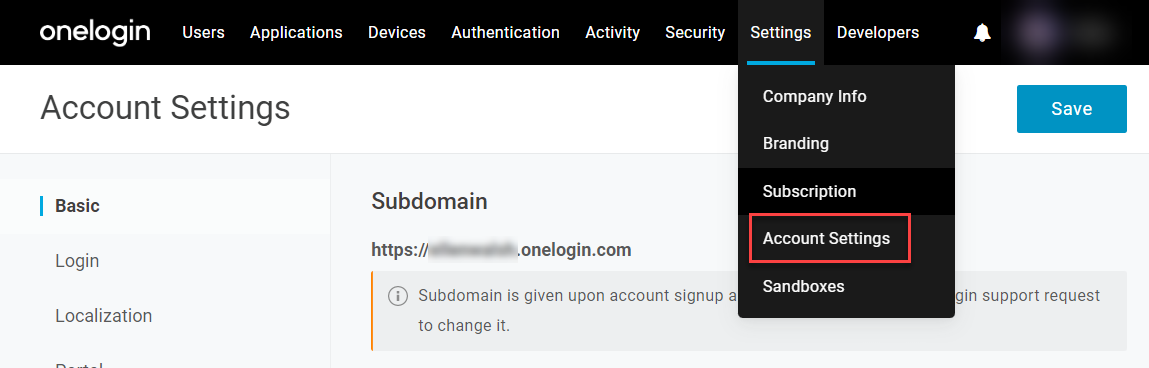
The Account Owner of a OneLogin tenant has exclusive access to account-level settings located the OneLogin admin portal under Settings > Account Settings. These options determine broadly-applied account policies that are unlikely to change frequently and should usually be configured during during your initial OneLogin setup.
Basic
Subdomain
This displays your unique OneLogin URL. Your URL's subdomain is chosen when you sign up for OneLogin and cannot be changed in your account settings. Speak with OneLogin Support or your account representative if you want to alter your URL.
SAML Apps
This setting disables the ability to manually edit the Login field in SAML connections, populating it programatically instead.
Assuming Users
|
Allow assuming users
|
This setting allows you and your administrators to assume user accounts, giving you limited access to and control over a user's account as if you're signed in as that user. This can be useful for troubleshooting and account management.
|
|
Allow external assuming
|
Similarly, this setting allows OneLogin Support to assume your account in order to diagnose and troubleshoot account issues.
|
OpenID
This setting is not related to OpenID Connect (OIDC), but rather enables the legacy OpenID protocol username generation. We recommend disabling this option on newer accounts.
DUO Universal Prompt
This setting activates the Universal Prompt flow for authenticating with Duo Security.
Framing Protection
These settings allow you to customize which websites, if any, are permitted to inline frame (iframe) your OneLogin admin and end user consoles.
Warning: It's difficult to identify all instances of OneLogin being iframed, since it's not possible to identify every instance of a 3rd-party iframe. It is important that only your company's trusted domains be permitted to use iframes in order to prevent clickjacking attacks.
Note: Changes to iframe settings may take up to 20 minutes to take effect in the system.
|
Disallow all framing
|
Select this setting to prohibit iframing with OneLogin
|
|
Allow all framing regardless of origin
|
This setting is deprecated and should not be selected.
|
|
Allow framing from the following origins
|
Select this setting to allow only the websites you specify to use iframes with OneLogin.
|
|
Content Security Policy - Origin URLs
|
Enter one or more URLs, separated by spaces, to allow as framing origins.
Note: All URLs are automatically converted into their origin format, with any part of the URL following the top-level domain removed. For example, https://www.website.com/page-3 will be treated as https://www.website.com.
|
These fallback settings were designed for users of Internet Explorer, which is no longer supported by OneLogin as of March 10, 2023, and may be disregarded.
Cookie Management
This setting gives your users' access to the Cookie Preference Center, allowing them to choose which cookies OneLogin is permitted to store in their browsers. You should generally enable this setting if you or any of your end users are subject to the General Data Protection Requirement (GDPR) of the European Union.
Deactivate Account
Only select this option to permanently delete this OneLogin tenant for you and all your users. Once deactivated, you and your users will no longer be able to access any of your company apps through OneLogin.
Warning: If you have applications configured to use SAML or OIDC through OneLogin, you may be locked out from these accounts. Verify that you have direct access to all necessary apps before deleting your OneLogin tenant.
Important: After confirming account deletion, you must remain on the page for at least 15 seconds for the process to finish. If you close the window or navigate away too quickly, the account will not be deleted.
If account deletion fails, there may be provisioning tasks or other operations pending that are blocking the deletion. Complete these steps and attempt termination again:
- Delete any mappings that may be automatically initiating pending tasks.
- License any users awaiting approval.
- Use a bulk operation to delete all user accounts except the account owner.
- Delete any app connectors that may be blocking the operation.
Login
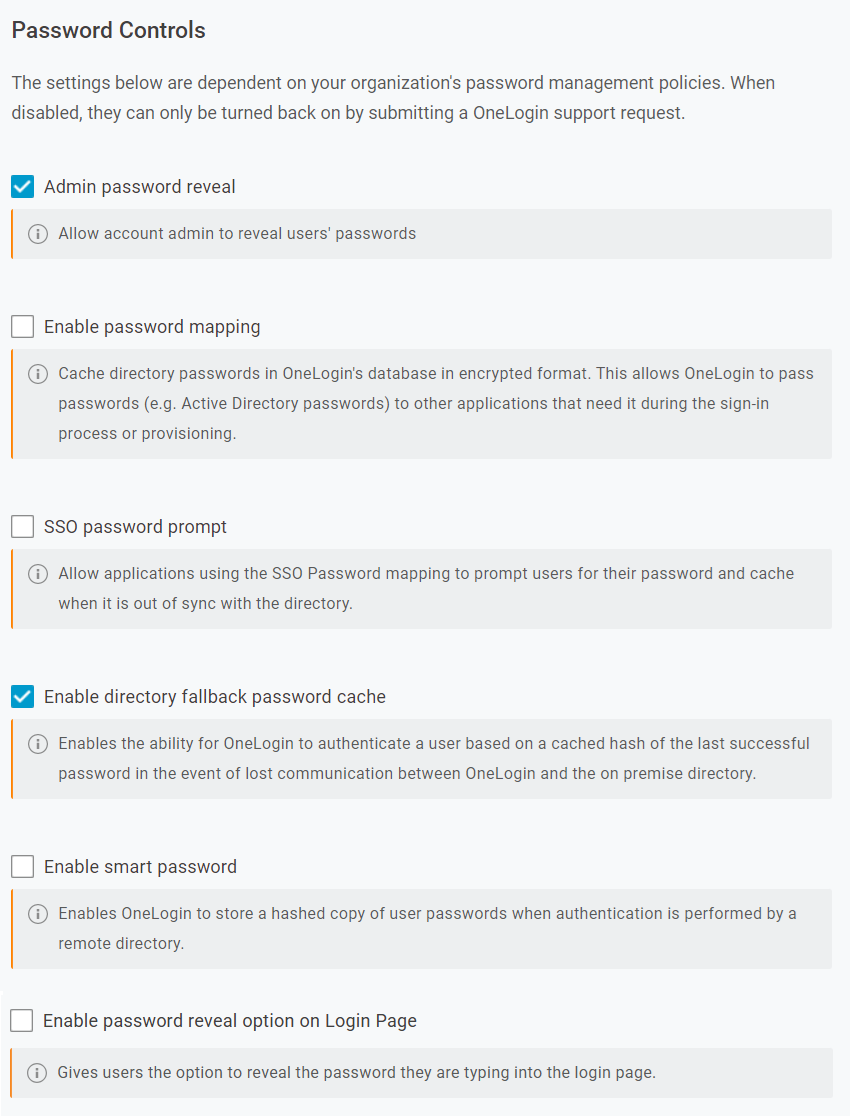
Password Controls
Note: Use caution when disabling settings that are enabled by default; these settings can only be re-enabled by contacting OneLogin Support.
|
Admin password reveal
|
Allows admins to view users' application passwords for company apps that use form-based authentication.
|
|
Enable password mapping
|
Allows OneLogin to securely synchronize specific application passwords with the user's directory password. To apply it to an app, set an app parameter that maps the app's Password attribute to SSO Password; the users' credentials for that app will automatically change whenever their OneLogin credentials change.
Note: Enable directory fallback password cache must be enabled in order to use this setting; enabling SSO password prompt is recommended as well.
|
|
SSO password prompt
|
Allows applications that have had SSO mapping configured to prompt users for their password when it's out of sync with the directory
|
|
Enable directory fallback password cache
|
Allows OneLogin to securely cache users' last successful password and use it for authentication if unable to contact the directory
|
|
Enable smart password
|
Allows OneLogin to provision user passwords from one directory to another, streamlining the migration process between the two
|
|
Enable password reveal option on Login Page
|
Allows Account Owners to enable or disable the password reveal button on the Login page.
|
Password Block List
Enter any text to prohibit specific users from including it in their passwords. Blocked passwords are not case-sensitive and check for partial matches. For example, blocking temp will also block Temporary123. To apply this feature to a user, assign them to a user policy with Enforce account password blocklist enabled.
Note: The blocklist is only applied to new passwords; it does not audit existing passwords that were set prior the policy being applied. If you want to ensure all users adhere to the new blocklist immediately, you can use a bulk operation to Force Password Reset for your users and prompt them to change their password the next time they log in.
Multi-step Login
Multi-step login enables OneLogin to request users' username and password in separate prompts, creating a more secure login experience and supporting many OneLogin authentication features. All accounts created after 2020 have this enabled by default.
We do not recommend disabling this feature without consulting your OneLogin representative to ensure that your current authentication process does not rely on multi-step login.
Logout URL
Enter an address where users will be redirected after logging out instead of returning to their login prompt.
Localization
To best support international users, you can enable localization to select the default language applied to new users' OneLogin portals and any additional languages you'd like to make available for them to change their accounts to. When localization is disabled, the OneLogin portal defaults to the user's browser settings to determine language.
Note: The localization default language only applies to user portals; the admin portal is not affected.
Portal
Personal Applications
This setting allows users to add and store passwords for their own apps in their OneLogin portal. Users can use personal apps to manage logins for hotels, airlines, LinkedIn, TripIt and even Facebook and Twitter. This gives end users more value out of OneLogin, which will drive usage and adoption of any company apps added to OneLogin.
Profile Page
This setting allows users to upload and use their own profile pictures in OneLogin.
Secure Notes
This setting allows users to record and save secure notes in their OneLogin profiles.
Password Notification
This setting displays a banner notification to OneLogin directory users five days before their password expires, providing them with a link to change their password.
Notifications
Add one or more email addresses, separated by commas, for any interested parties you want to ensure receive notification emails for security-related events in OneLogin.
|